[bannerTop]
Welcome to our Fulltab.com “Virus” removal guide. The following instructions will aid you in removing the unwanted software from your PC.
Today we are going to discuss a program identified as a browser hijacker. Its name is Fulltab.com “Virus” and it could cause the following changes to any and all of your browsers:
- Your default search engine and homepage could be substituted by new ones, which you are not used to seeing.
- A great number of online ads (banners/ pop-ups/ boxes) could be generated once the program has infected your PC. Sometimes they can make the entire browsing process impossible, because there may simply be too many of them.
- Some redirecting might occur every time you try to load a website, which may annoy you even further.
In general, such software is not among the dangerous malicious types and we are going to explain why below. Although no dangerous process could occur as a result of the infection with Fulltab.com “Virus” (or any other hijacker version), such a program might really “hijack” all your browsers. Neither Firefox, nor Explorer and Chrome are safe, as all of them could face some modifications due to the presence of a browser hijacker inside your system. To be completely precise, your browser programs are the only components of your system that any hijacker could access. All other apps, programs and data in general are inaccessible for such software. In fact, the changes mentioned above are the only ones Fulltab.com might result in once your PC has been infected by it.

What else could Fulltab.com do to you and your PC?
Actually, the only rather questionable aspect of any hijacker’s behavior while inside your system, is these programs’ ability to use your browser history records in order to conclude what type of ads and redirects you could be more willing to be interested in. Consequently, all the pop-ups and redirects that you may see and experience will be matched to the information derived from your browsing history. In fact, some users consider such an extensive browser history research quite intrusive. As a result, browser hijackers are considered to be potentially unwanted programs. Although Fulltab.com possesses all the aforementioned disturbing features, all of them are quite harmless. To be completely precise, we can conclude that Fulltab.com represents a program oriented towards advertising and promotion. It serves the marketing industry in the same way the radio and TV advertisements do. Really, there is nothing malicious about it. And to prove that, we are going to compare it to a version of file-locking Ransomware, so that you will know how much these two types of software really differ from each other. For example, one of the most serious differences is that any Ransomware type is able to get installed on your computer immediately and no permission and/or approval is required from your side. You will see below that Fulltab.com can NEVER do that – this software will always need you to accept the installation process. Another ultimate difference is that Ransomware could access the entire content of your disks and drives, while the hijackers’ access is limited to the history records of your browsers. Fortunately, hijackers could never be regarded as hazardous and malicious, though they might really be a pain in the neck.
Where you may come across hijackers
In this paragraph we are going to explain how you are most likely to end up infected with a hijacker. Despite the fact that hijackers are quite common and could be found inside torrents, shareware and spam, there is one source that still tops the charts with the most regular ones. This is the famous process bundling. Each result of this process is named a bundle and consists of numerous apps and programs. Developers use such interesting free mixes to attract your attention to the point that you will be willing to disregard the details of the installation process and perform it in the wrong way in your desire to use a program from a given bundle as soon as possible. In order to stay safe, just perform the best possible installation process. Such could only be achieved through the Advanced and the Customized wizard features. All the others are NOT recommended. The ones you need to especially avoid are called Default and Automatic. Don’t use them and your system could be safe even from threats as serious as Trojans to some extent. Such an infection could be removed if you are careful enough and you have the right guide at your disposal. Fortunately, we have attached it to our article. All you need to do is scroll down and implement all the steps there as carefully as possible.
Fulltab.com “Virus” Removal
I – Uninstallation
[bannerMiddle]
- Use the Winkey+R keyboard combination, write Control Panel in the search field and hit enter.

- Go to Uninstall a program under Programs.

- Seek the unwanted software, select it and then click on Uninstall
- If you are unable to spot Fulltab.com, search for any unrecognized programs that you do not remember installing on your PC – the unwanted software might disguise itself by going under a different name.
II – Safe mode and revealing hidden files
III – Cleaning all your browsers
- Go to your browser’s icon, right-click on it and select Properties.

- Go to the Shortcut tab and in the Target make sure to delete anything written after “.exe”.

- Now, open your browser and follow the instructions below depending on whether you are using Chrome, Mozilla or IE.
- Chrome users:
- Go to your browser’s main menu located in the top-right corner of the screen and select Settings.
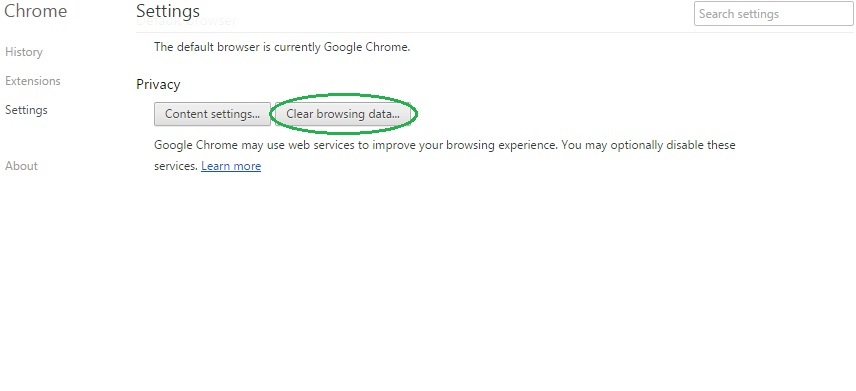
- Scroll down, click on Show Advanced Settings and then select Clear browsing data. Just to be sure, tick everything and clear the data.
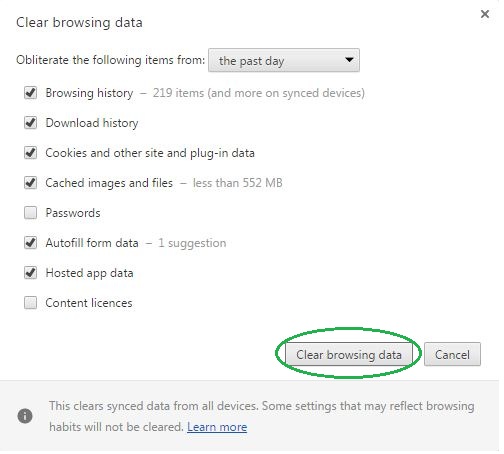
- Now, in the left pane, go to Extensions and look through all extensions that are integrated within your browser. If you notice any suspicious add-on, disable it and then remove it.
- Firefox users:
- Similarly to Chrome, go to the main menu and select Add-ons and then Extensions.
- Remove any suspicious browser extensions that you may have even if they do not have the name Fulltab.com on them.
- IE users:
- Go to Tools and select Manage add-ons.

- Click on all add-on types from the left pane and check if there is anything suspicious in the right panel. In case you find anything shade, make sure to remove it.
IV – Removing Shady processes
[bannerMiddleSecond]
- Go to your start menu, type Task Manager in the search field and from the results open View running processes with Task Manager.

- Thoroughly look through all processes. The name Fulltab.com might not be there, but if you notice any shady looking process that consumes high amounts of memory it might be ran by the unwanted program.
- If you spot the process ran by Fulltab.com, right-click on it, open its file location and delete everything in there. Then go back to the Task Manager and end the process.

V – DNS check
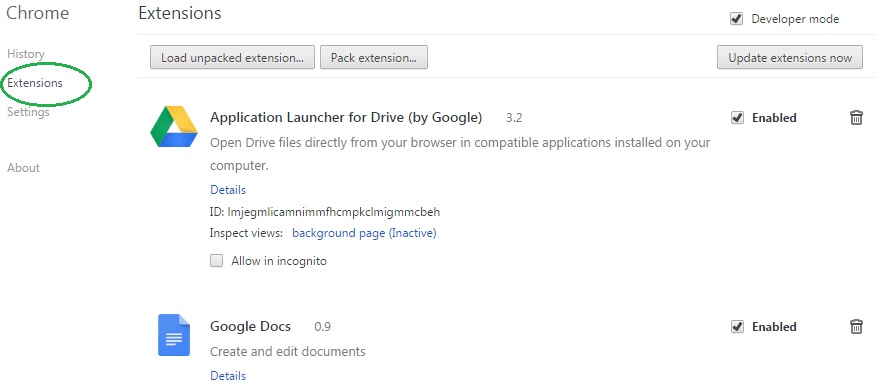
- In the start menu search box write View Network Connections and open the first result.
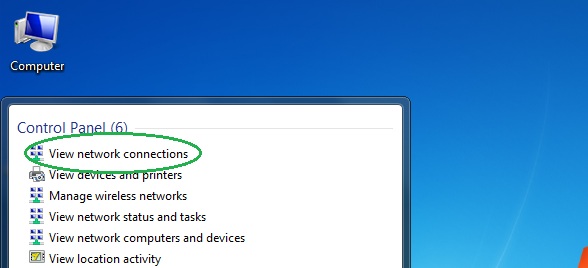
- Right-click on the network connection you are using and go to Properties.

- Select Internet Protocol Version (TCP/IPv4) and click on Properties.

- If Obtain DNS server addresses automatically is not checked, check it.
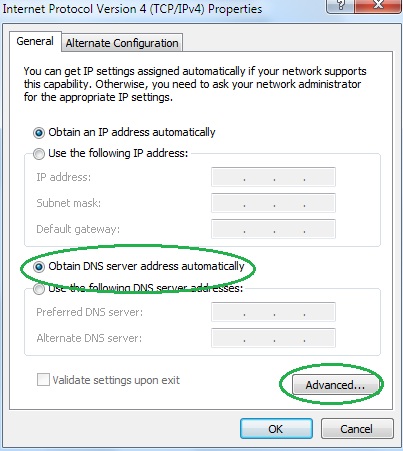
- Go to Advanced and select the DNS If there is anything in the DNS server addresses field, remove it and click OK.

- Click OK on the rest of the opened windows.





Leave a Reply