[bannerTop]
Welcome to our All-czech.com Virus removal guide. The following instructions will aid you in removing the unwanted software from your PC.
If a program called All-czech.com has invaded your Chrome, IE or Firefox browser and has changed its normal search engine and default homepage or started redirecting your online searches, here you can find all the information you might need in order to handle the situation and remove the unwanted software that has implemented those changes. From the following article you will learn what programs such as All-czech.com are primarily used for, how problematic they can be and how you can ensure the safety of your PC from now on, so that no more unwanted software like this one gets installed on it. As far as the removal of the invasive program is concerned, you can find instructions on how to uninstall the application and fully get rid of it down below the article, in our removal guide manual.
Browser Hijackers and online advertising
All-czech.com is only one of the more recent examples of a software type known as Browser Hijackers. Generally, all programs that are intrusive and tend to mess with the user’s browser fall under this category. Most of the time, the purpose of such applications is connected with the internet advertising industry. They are used as a way to promote other products, websites, online services, etc. However, the problem is the advertising methods most Browser Hijackers utilize. Unlike other forms of online marketing, Browser Hijackers are all about being as obstructive and invasive as possible, often resorting to invasion of the user’s personal space. This is what makes them quite undesirable and frustrating to have on your PC. Additionally, they hardly ever provide you with any actual functionality to compensate for their negative traits. All in all, if a Browser Hijacker has gotten on your machine, the best course of action is almost always uninstalling the nagging application and getting rid of all its files that are on your hard drive.
Comparing it to viruses
It sure is frustrating to have some undesirable program installed onto your computer, which tries to modify your browser and nag you with intrusive advertising content. However, it is necessary to note that applications like All-czech.com are far from actual malicious software threats such as Trojan horses or Ransomware. Here is a brief comparison between Browser Hijackers and actual viruses that will show you the main differences between the two.
- A lot of Browser Hijackers are legal pieces of software – PC viruses are always illegal and illegally distributed
- Most programs like All-czech.com, though invasive and obstructive, would not try to damage your system – actual PC viruses can corrupt or delete system files and the infamous Ransomware type can lock your data and demand a ransom payment afterwards.
- Browser Hijackers do not try to hide their presence (quite the opposite). While they might sometimes be difficult to remove, their symptoms are almost always very easy to spot and recognize. – most types of PC viruses are programmed in such a way so that they are as difficult to detect as possible, oftentimes showing little to no symptoms.
Hopefully, this brief comparison has shown you why All-czech.com is probably not something you should be overly worried about. Just make sure to be careful until the unwanted software is removed.
What Browser Hijackers CAN do
A program of this type might not try to damage system data or lock your personal files but it is still capable of causing quite a bit of trouble which is the reason why removing it is necessary.
- They can flood your browser with all sorts of sketchy banners, shady links and obstructive pop-ups. Even if the aggressive advertising materials are legit and not dangerous, they can still make your online experience miserable. We advise to keep away from the ads until the Hijacker is removed.
- Some Browser Hijackers use different methods to track your browsing activity in order to gather valuable marketing data. The information can later be sold to third-parties or directly employed within the displayed ads, thus making them more relevant to your personal interests.
- A significant PC slow-down can occur due to heavy CPU and RAM consumption caused by the processes of the Hijacker. This is especially common among less powerful computers.
Helpful guidelines
Here, we have a short list of some very important safety rules that everyone should know and utilize, in order to keep their machine safe from any potentially unwanted programs and software threats:
- Never open .exe files (or any other files for that matter) if you are not sure where they came from or whether or not they are safe.
- Set your browser to always ask for a permission from you prior to downloading files to your PC.
- Be on the safe side while browsing the internet. If you are not sure that a certain website is safe, make sure to avoid it!
- Spam e-mails are a common way of spreading Browser Hijackers, so be careful not to open or interact with letters that seem to be spam.
- A reliable scanner or anti-malware/adware tool can greatly improve your PC’s protection!
- Pay close attention to the installation menu of new programs you’re about to install. Make sure that you are well aware of whether and what added applications there are to the main piece of software. If there’a anything added that looks sketchy and suspicious, be sure to uncheck it before installing the program you want. If you have access to an Advanced installation menu, make use of it because there you will be able to see everything that has been added to the software bundle and leave out whatever you might not want to have installed on your PC.
SUMMARY:
| Name | All-czech.com |
| Type | Browser Hijacker |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Symptoms | Nagging online ads, browser changes such as new search engine and changed homepage, PC slowdown. |
| Distribution Method | Different forms of spam, torrent websites, Internet banners/pop-ups, software-bundling. |
All-czech.com Removal
I – Uninstallation
[bannerMiddle]
- Use the Winkey+R keyboard combination, write Control Panel in the search field and hit enter.

- Go to Uninstall a program under Programs.

- Seek the unwanted software, select it and then click on Uninstall
- If you are unable to spot All-czech.com, search for any unrecognized programs that you do not remember installing on your PC – the unwanted software might disguise itself by going under a different name.
II – Safe mode and revealing hidden files
III – Cleaning all your browsers
- Go to your browser’s icon, right-click on it and select Properties.

- Go to the Shortcut tab and in the Target make sure to delete anything written after “.exe”.

- Now, open your browser and follow the instructions below depending on whether you are using Chrome, Mozilla or IE.
- Chrome users:
- Go to your browser’s main menu located in the top-right corner of the screen and select Settings.
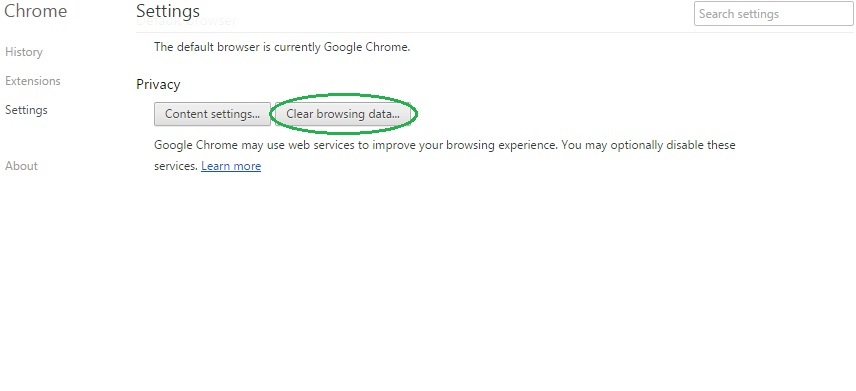
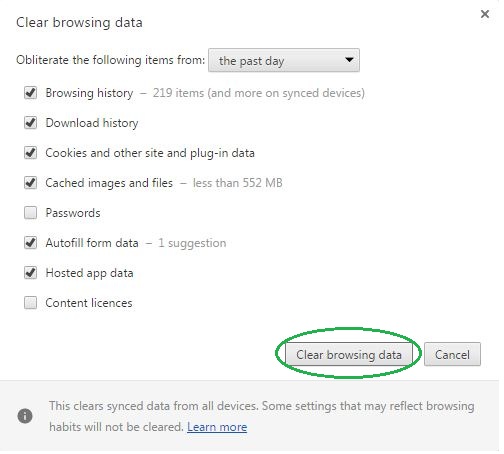
- Scroll down, click on Show Advanced Settings and then select Clear browsing data. Just to be sure, tick everything and clear the data.
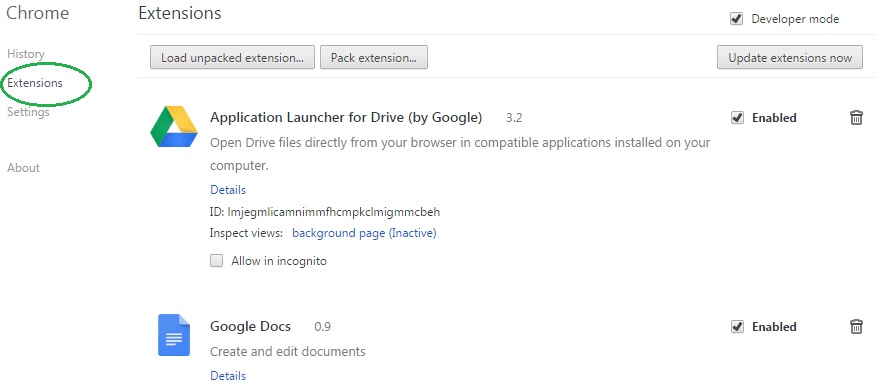
- Now, in the left pane, go to Extensions and look through all extensions that are integrated within your browser. If you notice any suspicious add-on, disable it and then remove it.
- Firefox users:
- Similarly to Chrome, go to the main menu and select Add-ons and then Extensions.
- Remove any suspicious browser extensions that you may have even if they do not have the name All-czech.com on them.
- IE users:
- Go to Tools and select Manage add-ons.

- Click on all add-on types from the left pane and check if there is anything suspicious in the right panel. In case you find anything shade, make sure to remove it.
IV – Removing Shady processes
[bannerMiddleSecond]
- Go to your start menu, type Task Manager in the search field and from the results open View running processes with Task Manager.

- Thoroughly look through all processes. The name All-czech.com might not be there, but if you notice any shady looking process that consumes high amounts of memory it might be ran by the unwanted program.
- If you spot the process ran by All-czech.com, right-click on it, open its file location and delete everything in there. Then go back to the Task Manager and end the process.

V – DNS check
- In the start menu search box write View Network Connections and open the first result.
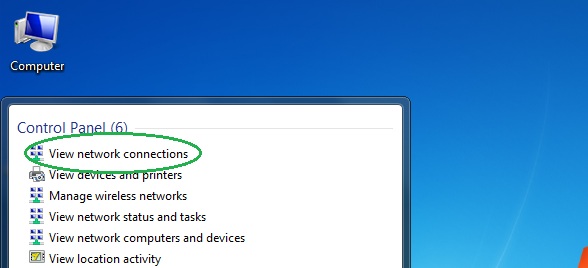
- Right-click on the network connection you are using and go to Properties.

- Select Internet Protocol Version (TCP/IPv4) and click on Properties.

- If Obtain DNS server addresses automatically is not checked, check it.
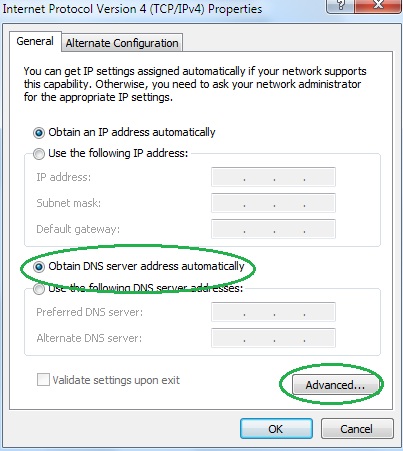
- Go to Advanced and select the DNS If there is anything in the DNS server addresses field, remove it and click OK.

- Click OK on the rest of the opened windows.





Leave a Reply