[bannerTop]
Welcome to our Cryptobyte Ransomware removal guide. The following instructions will aid you in removing the unwanted software from your PC for free.
Not many users are aware of just how important it is to keep their files backed up. Most people feel comfortable having their data stored only on their PC’s hard drive and believe that nothing can get to it. However, this is a very big mistake that gets oftentimes exploited by hackers. There is a whole class of software viruses called Ransomware that prey on the lack of data backup among the majority of users. Today, we will be talking about Cryptobyte, which is one of the latest and most advanced viruses that fall under the Ransomware category. Similarly to its predecessors, this evil piece of malware is able to use encryption to lock the files of its victims and ask for a ransom payment once its job is finished. While there are certain possible methods to unlock the data without having to pay the ransom, it oftentimes depends on the specific situation. We can offer you a potential Cryptobyte Ransomware removal and file decryption method for those of you who have already had their documents encrypted, but we cannot guarantee that it would be successful in all possible scenarios. However, we believe that paying the ransom is a very bad idea and it is always worth seeking an alternative solution to the Ransomware problem.
It is difficult to detect Ransomware
Nowadays, it seems that viruses the likes of Cryptobyte are some of the most dangerous and widely spread software threats that one can encounter. A major reason for that is the fact that they are extremely difficult to spot once they get inside one’s computer. Typical Ransomware such as Cryptobyte almost always remains totally undetected by most regular antivirus programs. This has to do with the fact that most Ransomware viruses do not actually try to harm anything on the victim’s PC. In most cases, no actual damage is being done. Encryption, which is the preferred file-locking method, is, in fact, a legit type of process and commonly used for file protection. The problem is that when Ransomware uses encryption to lock your personal data, your security software will likely not be able to recognize that as a threat and prevent the process from being completed. Basically, this is how Cryptobyte and other malware of its type are able to prevent users from accessing their own data without being detected until the encryption is finished.
After the data has been locked, the virus would actually display a notification on the screen of the infected computer. The message usually informs the user that the only way they could restore their access to their own files is to pay a certain amount of money (usually in the form of bitcoins) by following a specific set of instructions provided within the said message. The reason why the preferred payment currency is bitcoins is due to the fact that they are untraceable and thus the hacker would be able to remain anonymous even after the payment has been made.
Be on the lookout for those symptoms!
Manual Ransomware detection is not always possible. In many cases Cryptobyte will have little to no symptoms, and even when there are certain signs of infection, they would be very difficult to spot. However, each of your readers should still have a general idea about the possible indications of a Ransomware attack. Being observant and watchful is always a good thing and therefore we advise you to always keep an eye on what’s going on with your computer.
- Increased CPU and RAM usage is commonly accredited to a malware infection. Of course, this can be caused by a whole lot of other possible issues, yet still, if you notice any sudden and unexpected upsurge of system resource consumption, know that it might be Ransomware.
- During the encryption period, observant users might notice that their free HDD space is less than it should be. If you, too, notice this, there is a very high chance that there is a Ransomware virus on your PC since this is one of the most typical symptoms.
- Generally, if your machine is acting weird, experiencing sudden freezes, crashes or seems to have significantly slowed-down in terms of productivity, there is probably something that is not quite right. In those cases, it won’t hurt to make use of our Cryptobyte removal guide, just in case there is Ransomware on the computer.
How to keep your PC safe and your data protected from Ransomware
To make sure that our readers know how to avoid any future Cryptobyte attacks, we have devised a list of rules and guidelines aimed at increasing the security levels of their computers and personal data.
- Customize your browser’s settings in order to make it impossible for any files to be downloaded automatically without your permission.
- Never turn off your firewall and antivirus program for long periods of time or your computer might get exposed to Trojan horse attacks. Bear in mind that Trojans are one of the top most widely used methods of infecting computers with Ransomware, because they can be used as a backdoor.
- As we mentioned in the beginning of the article, not having a backup of your valuable data is a huge mistake. If you haven’t already backed-up your files, be sure to do it ASAP!
- Shady sites with obnoxious banners and spam messages are two more very common Ransomware distribution methods. This is why you must always be on your guard when surfing the Internet – one misclick and your whole data might get encrypted in a matter of seconds.
- If you suspect a Ransomware infection on your computer, do not connect to it any other devices or you’d risk having them infected as well.
Cryptobyte Ransomware Removal
Here is what you need to do in order to remove a Ransomware virus from you computer.
I – Reveal Hidden files and folders and utilize the task manager
[bannerMiddle]
- Use the Folder Options in order to reveal the hidden files and folders on your PC. If you do not know how to do that, follow this link.
- Open the Start Menu and in the search field type Task Manager.
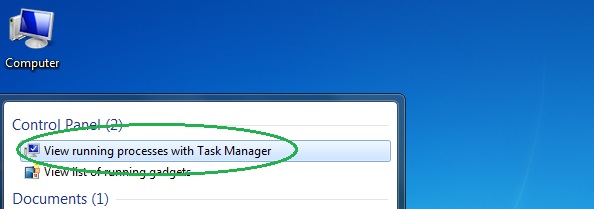
- Open the first result and in the Processes tab, carefully look through the list of Processes.
- If you notice with the virus name or any other suspicious-looking or that seems to consume large amounts of memory, right-click on it and open its file location. Delete everything in there.
[bannerMiddleSecond]

- Make sure that the hidden files and folders on your PC are visible, else you might not be able to see everything.
- Go back to the Task Manager and end the shady process.
II – Boot to Safe Mode
- Boot your PC into Safe Mode. If you do not know how to do it, use this guide/linked/.
III – Identify the threat
- Go to the ID Ransomware website. Here is a direct link.
- Follow there in order to identify the specific virus you are dealing with.
IV – Decrypt your files
- Once you have identified the virus that has encrypted your files, you must acquire the respective tool to unlock your data.
- Open your browser and search for how to decrypt ransomware, look for the name of the one that has infected your system.
- With any luck, you’d be able to find a decryptor tool for your ransomware. If that doesn’t happen try Step V as a last ditch effort to save your files.
V – Use Recuva to restore files deleted by the virus
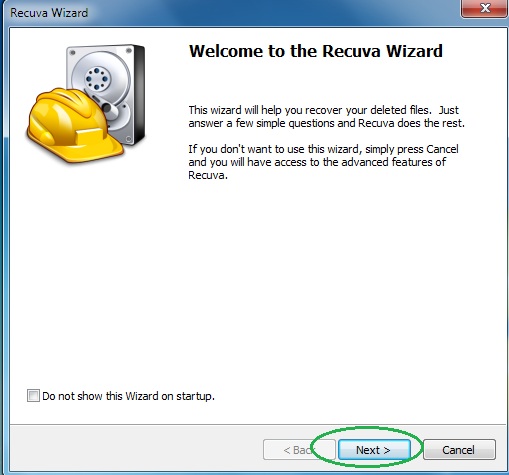
- Download the Recuva tool. This will help you restore your original files so that you won’t need to actually decrypt the locked ones.
- Once you’ve downloaded the program, open it and select Next.
- Now choose the type of files you are seeking to restore and continue to the next page.
- When asked where your files were, before they got deleted, either use the option In a specific location and provide that location or choose the opt for the I am not sure alternative – this will make the program look everywhere on your PC.

- Click on Next and for best results, enable the Deep Scan option (note that this might take some time).
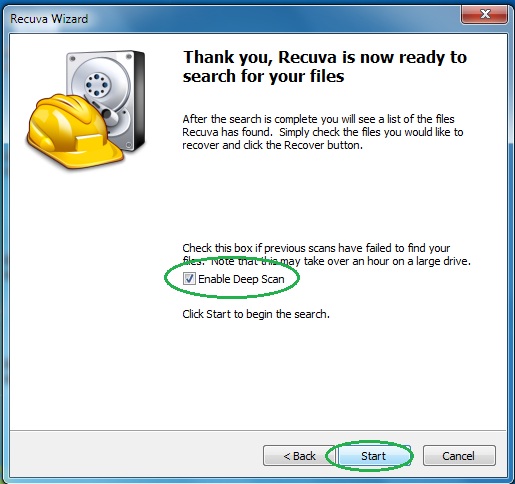
- Wait for the search to finish and then select which of the listed files you want to restore.
