[bannerTop]
Welcome to our [email protected] Ransomware removal guide. The following instructions will aid you in removing the unwanted software from your PC for free.
If you landed on this site, you have probably encountered a Ransomware cryptovirus named [email protected] Ransomware. This cryptovirus is involved in a particular from of a cybercrime, which keeps the files, found on your computer, hostage with a secret encryption and asks you to pay ransom for a decryption key. To help you better understand this infection, in the next lines, we will explain to you its typical behavior, infection and distribution methods and we will try to also help you to remove the nasty malware. For that, we have published a free guide, which aims to assist you in the detection and the safe removal of [email protected] Ransomware as well as the restoration of some of your files. We hope you will find the information that follows helpful and will make the most of it in order to minimize the negative effects of the Ransomware.
Did [email protected] Ransomware corrupt your files?
Probably you have already heard that Ransomware infections like [email protected] Ransomware can be really bad for your PC and especially your data. But how exactly can this malware cause you harm? Well, unlike most of the viruses, which can destroy or delete your files, once they infect you, a Ransomware cryptovirus does not do that. Instead, it uses a special encryption algorithm to render the files inaccessible. What the encryption does is, it converts them into some unreadable combinations of symbols, which cannot be recognized or opened by any program. They are still on the computer, but the hackers, who control the Ransomware, keep them hostage for ransom. If the users want to regain the access to the encrypted files, they have to pay for a special decryption key, which is supposed to reverse the harmful encryption. This is a very nasty criminal “business model”, which makes the criminals rich on the back of the desperate victims.
How did you get infected?
According to the latest reports, an infection with [email protected] Ransomware may occur when the users click on some malicious transmitter. Spam messages, different email attachments, misleading links or fake ads, torrents and shady installers, are among the most commonly used transmitters of such infections. That’s why the security experts advisable the users to restrict their interaction with such content and to be cautious if different pop-ups appear on their screen and prompt them to click or download something. In some cases, the Ransomware may come in a combo with a Trojan horse and use its cover to sneak inside the system. What is really tricky about this malware is that it operates silently, almost without symptoms, and reveals itself with a scary ransom note only after all the files are completely encrypted.
Is there any way to break the encryption and restore the files?
Yes, there is. Once [email protected] Ransomware applies its encryption, it also generates a special decryption key, which can reverse it. That decryption key, however, is with the hackers and this is what they ask ransom for. The ransom is usually demanded in Bitcoins, which is a special untraceable online currency, which helps the criminals to remain undetected. In case that the victims want to decrypt their data, they have to strictly follow the instructions, shown in the ransom note. Very often, a short deadline is given, after which the ransom may double or the decryption key may get destroyed. All these are manipulative tactics, which aim to make the users feel desperate and pay the ransom as quickly as possible.
Before you decide how to act, stop and think about the risk!
Many professionals, experienced in dealing with Ransomware and its consequences, advise the users not to act out of fear and confusion and to seek for safer alternatives than the ransom payment. The thing is that paying the ransom may turn into a real bad deal for the victims because they may lose their money for nothing. It is very likely that the cybercriminals may simply skip the part with sending the decryption key and just disappear with the money once they get them. And there is really nothing worse than making the crooks rich and still having to deal with the nasty encryption.
How to remove the [email protected] Ransomware infection?
While the Ransomware is still not removed, you should not consider your system safe. The PC could be easily compromised by some other virus, and the hackers may mess up with it as they please. That’s why eliminating [email protected] Ransomware and all of its traces is a good way to start dealing with the infection. The guide below contains the exact steps for that and we encourage you to follow them as they are shown. If you are not confident enough to handle the manual, think about using the removal tool. There are also some instructions that may eventually help you restore some of your data. Check them out and let us know if you have any questions.
[email protected] Ransomware Removal
Here is what you need to do in order to remove a Ransomware virus from you computer.
I – Reveal Hidden files and folders and utilize the task manager
[bannerMiddle]
- Use the Folder Options in order to reveal the hidden files and folders on your PC. If you do not know how to do that, follow this link.
- Open the Start Menu and in the search field type Task Manager.
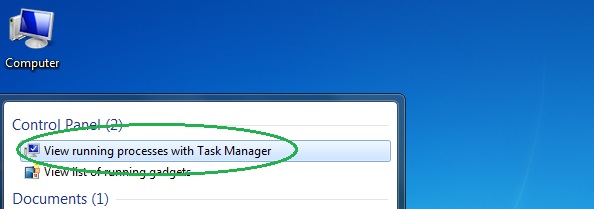
- Open the first result and in the Processes tab, carefully look through the list of Processes.
- If you notice with the virus name or any other suspicious-looking or that seems to consume large amounts of memory, right-click on it and open its file location. Delete everything in there.
[bannerMiddleSecond]

- Make sure that the hidden files and folders on your PC are visible, else you might not be able to see everything.
- Go back to the Task Manager and end the shady process.
II – Boot to Safe Mode
- Boot your PC into Safe Mode. If you do not know how to do it, use this guide/linked/.
III – Identify the threat
- Go to the ID Ransomware website. Here is a direct link.
- Follow there in order to identify the specific virus you are dealing with.
IV – Decrypt your files
- Once you have identified the virus that has encrypted your files, you must acquire the respective tool to unlock your data.
- Open your browser and search for how to decrypt ransomware, look for the name of the one that has infected your system.
- With any luck, you’d be able to find a decryptor tool for your ransomware. If that doesn’t happen try Step V as a last ditch effort to save your files.
V – Use Recuva to restore files deleted by the virus
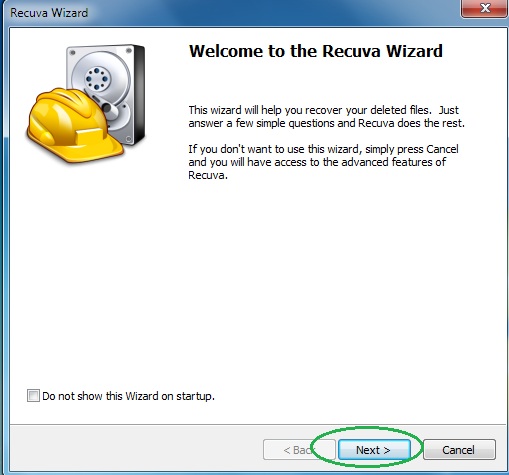
- Download the Recuva tool. This will help you restore your original files so that you won’t need to actually decrypt the locked ones.
- Once you’ve downloaded the program, open it and select Next.
- Now choose the type of files you are seeking to restore and continue to the next page.
- When asked where your files were, before they got deleted, either use the option In a specific location and provide that location or choose the opt for the I am not sure alternative – this will make the program look everywhere on your PC.

- Click on Next and for best results, enable the Deep Scan option (note that this might take some time).
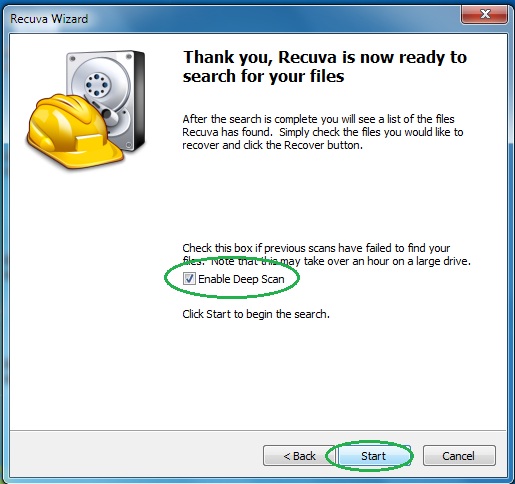
- Wait for the search to finish and then select which of the listed files you want to restore.






Leave a Reply