[bannerTop]
Welcome to our .Pumas Ransomware removal guide. The following instructions will aid you in removing the unwanted software from your PC for free.
Are you unable to access some or most of your files? Or, when you try to open any document, your screen displays a strange ransom-demanding note? If yes, then this is a sure sign that your computer has been attacked by a Ransomware infection. The infections of the Ransomware type are famous for their ability to block the users’ access to their data or to the screen of their device. They either apply a complex file encryption to the data or place a scary ransom-demanding banner all over the monitor of the infected machine. If something similar has happened to you and you are unable to understand why are you getting such notifications and why your files have suddenly became completely inaccessible, then you need really tp familiarize yourself with the impact of the Ransomware and its attack.
You may not have no idea about how to deal with this sort of malware and its consequences but after you read this article, we believe you will gain a better understanding about your alternatives and the possible courses of action you could take. In the next paragraphs, we will discuss in detail the specifics of Ransomware and will provide you with a Removal Guide for one recently detected representative of this virus group called .Pumas. In case your PC has been infected by this particular version of Ransomware, below you will find detailed guidance on how to remove the infection from your system. You will also find a helpful automatic removal tool and some tips for protection as well as suggestions for the restoration of your files from the nasty encryption that is keeping them inaccessible.
What is Ransomware? How harmful can a threat of this type be?
The Ransomware-based viruses are regarded as extremely harmful computer threats. The hackers who create such threats use them for a particularly nasty online blackmailing scheme which generates enormous profits from the unsuspecting web users. The way such cyber criminals make money is they use the malware to lock your files or the entire infected device. Then, they place a threatening ransom notification on the screen which requires of you to pay a certain amount of money in order to regain your access.
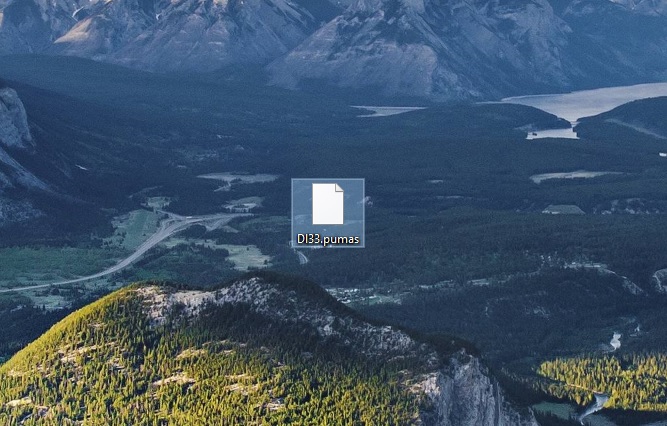
.Pumas, in particular, is a file encrypting Ransomware which is created by anonymous cyber crooks with the same illegal purpose – to take hostage of your files and blackmail you for their liberation. This malware mostly targets computers with Windows OS installed on them and tries to silently break through their security in various ways. The most frightening thing about the Ransomware threat is that it can infect you and install itself automatically in your system without any visible symptoms or indications.
To lock your files for its blackmail scheme, .Pumas typically uses a very complex and strong encryption algorithm which detects and encrypts documents, images, videos, audios, archives, databases and maybe even some system files. The malware may even change their extensions in order to prevent you from opening them with any software. Usually, after the harmful encryption has been applied, every time you try to open an encrypted file, you will receive error messages which will tell you to purchase a decryption key. The Ransomware may also try to scare you by displaying a ransom note which says that if you don’t pay within a certain time period, the decryption key will be deleted permanently from the hackers’ server and, without it, you will lose any chances of getting back your important files.
We should warn you not to give in to such threatening messages because this is a common intimidation tactic that hackers use in order ensure quick payment of the ransom sum. Know that even if you carry out the ransom payment nothing can really guarantee the successful liberation of your files. Only a full backup of your own can get them back. Decrypting them with the key sent from the hackers may not always work flawlessly. Not to mention that you may not even receive such a key from the crooks once they get your money.
For the time the Ransomware stays on the computer, though, it may cause several other problems such as very slow system response, hard drive failure, software malfunctioning and many more. Therefore, we suggest you remove .Pumas and clean your PC from its harmful scripts instead of giving your money to some anonymous hackers.
Methods of removing .Pumas
Ransomware is a very complex infection which may not always be completely curable. That’s why, it requires your full attention if you want to effectively remove it. One trusted method we can advise you to go for in order to clean your PC from all the hidden harmful scripts is to scan it with some professional antimalware software program such as the .Pumas removal tool posted below. Another method to deal with the infection is to use the manual Removal Guide we’ve posted on this page. Note that none of the methods can guarantee a 100% recovery from the encryption attack but at least with a clean computer you may safely give a try to some file-restoration alternatives or use your file backups without risk of getting the files encrypted again.
Source: Howtoremove.guide’s instructions Remove .Pumas Virus File Ransomware (+File Recovery)
Remove .Pumas Virus File Ransomware
Here is what you need to do in order to remove a Ransomware virus from you computer.
I – Reveal Hidden files and folders and utilize the task manager
[bannerMiddle]
- Use the Folder Options in order to reveal the hidden files and folders on your PC. If you do not know how to do that, follow this link.
- Open the Start Menu and in the search field type Task Manager.
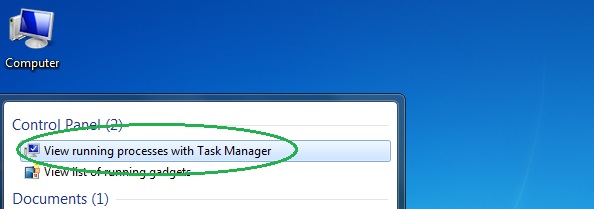
- Open the first result and in the Processes tab, carefully look through the list of Processes.
- If you notice with the virus name or any other suspicious-looking or that seems to consume large amounts of memory, right-click on it and open its file location. Delete everything in there.
[bannerMiddleSecond]

- Make sure that the hidden files and folders on your PC are visible, else you might not be able to see everything.
- Go back to the Task Manager and end the shady process.
II – Boot to Safe Mode
- Boot your PC into Safe Mode. If you do not know how to do it, use this guide/linked/.
III – Identify the threat
- Go to the ID Ransomware website. Here is a direct link.
- Follow there in order to identify the specific virus you are dealing with.
IV – Decrypt your files
- Once you have identified the virus that has encrypted your files, you must acquire the respective tool to unlock your data.
- Open your browser and search for how to decrypt ransomware, look for the name of the one that has infected your system.
- With any luck, you’d be able to find a decryptor tool for your ransomware. If that doesn’t happen try Step V as a last ditch effort to save your files.
V – Use Recuva to restore files deleted by the virus
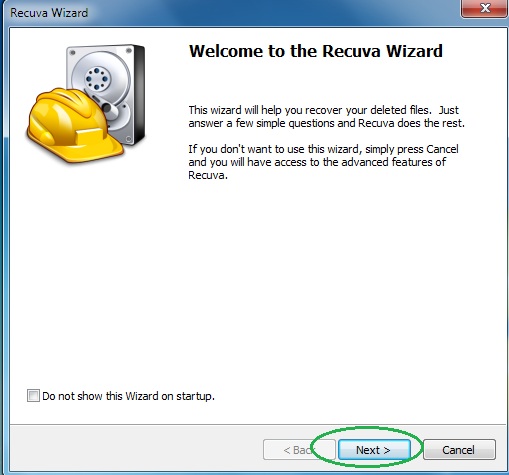
- Download the Recuva tool. This will help you restore your original files so that you won’t need to actually decrypt the locked ones.
- Once you’ve downloaded the program, open it and select Next.
- Now choose the type of files you are seeking to restore and continue to the next page.
- When asked where your files were, before they got deleted, either use the option In a specific location and provide that location or choose the opt for the I am not sure alternative – this will make the program look everywhere on your PC.

- Click on Next and for best results, enable the Deep Scan option (note that this might take some time).
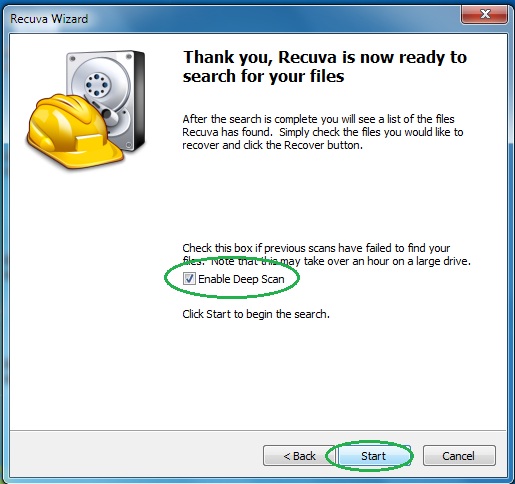
- Wait for the search to finish and then select which of the listed files you want to restore.






Leave a Reply