In this article we have written about .Cesar Virus Ransomware – a virus that belongs to the malicious software family of Ransomware and has likely even become the reason for file encryption of some really important data on your PC. But what does this evil category of malware really represent? The kind of programs in the Ransomware group are not just simple viruses. This dangerous category is also one of the fastest expanding virus families in the cyber world. There are three main subgroups:
- (MOBILE) SCREEN-LOCKING VIRUSES: they could target smartphones, laptops, desktop computers, tablets, and other portable devices, making you unable to unlock your screen and access anything on the infected device until you pay the needed ransom.
- RANSOMWARE USED AGAINST CYBER CRIMINALS: some of the official authorities might use Ransomware products to cope with dangerous online criminals. For example, the people who violate copyright policies or laws could be stopped from doing it, and are going to to pay for whatever wrong they have done with the help of programs like these. Nevertheless, that’s the only case when software like this is used properly and for decent purposes.;
- FILE-TARGETTING VERSIONS (also known as FILE-ENCRYPTING): that’s the most famous subtype of that malware. Its members are able to break into your system, and after that gather different details about the data you use most often. After the completion of that, these files are normally encrypted with a key that is really complex. After all of the files have been encoded, you will typically receive an awful notification to inform you how to pay the requested money.
Which subgroup of Ransomware does .Cesar Virus belong to?
It is a version of the data-targeting malware. The representatives of this subcategory usually conquer your system with or without the help of a Trojan, which is another version of malware. Generally, what actually happens is that the Trojan virus provides the passing of the Ransomware virus inside your PC. After both of these wicked programs have succeeded in entering your computer, they normally continue with their activities which are as follows – scanning of all your drives and encrypting the most frequently used data on them.
What may help in the fight against Ransomware?
Here is the bothering part of our article. Our purpose is not to discourage you in any way; on the other hand, we won’t delude you into thinking that it is easy or fast to remove an infection caused by Ransomware and for its effects to be reversed. Do not doubt that .Cesar Virus is positively the worst virus you may ever catch and its removal is not an easy task at all – it may require a lot of resources, attention to detail and special know-how. Consequently, we cannot just promise you will manage to successfully fight this virus, but we will share some methods and techniques you can use.
Our five recommendations:
- Don’t start fighting this Ransomware with any expectations. You should be ready to say goodbye to your data if it has no back-up. Maybe your system will need to be reinstalled to get rid of this virus.
- Check what kind of options you have, look for ways, read some articles on the Internet, ask people who are experts – understand what people have done to recover from malware like this.
- Consider the option of purchasing software, which has been designed to fight such threats, maybe it will solve your problem.
- Read our Removal Guide below. There are instructions which might be beneficial and result in the removal of .Cesar Virus and perhaps even the recovery of your files. On the other hand, once again, we cannot promise you anything.
- Finally – do not pay the ransom right after you have received the ransom-demanding alert. Do everything else which is possible.
The only solution that always works:
After your system has been infected, you do not have so many options and nothing can guarantee that your actions will be successful. Therefore, the moral of the entire story is the following:
- Whatever happens, save important data by backing it up as often as you can.
- Install and update the very best anti-virus tool you can find – such powerful programs may stop you from catching many other viruses.
- Simply ignore the potential sources of Ransomware, which could be many and various, but the most regular ones are illegal freeware or torrents; pretending-to-be system requests; fake ads; diverse emails and all other shady letters; all kinds of email attachments.
.Cesar Virus Ransomware Removal
Here is what you need to do in order to remove a Ransomware virus from you computer.
I – Reveal Hidden files and folders and utilize the task manager
[bannerMiddle]
- Use the Folder Options in order to reveal the hidden files and folders on your PC. If you do not know how to do that, follow this link.
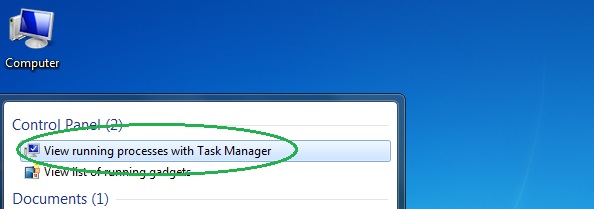
- Open the Start Menu and in the search field type Task Manager.
- Open the first result and in the Processes tab, carefully look through the list of Processes.
- If you notice with the virus name or any other suspicious-looking or that seems to consume large amounts of memory, right-click on it and open its file location. Delete everything in there.
[bannerMiddleSecond]

- Make sure that the hidden files and folders on your PC are visible, else you might not be able to see everything.
- Go back to the Task Manager and end the shady process.
II – Boot to Safe Mode
- Boot your PC into Safe Mode. If you do not know how to do it, use this guide/linked/.
III – Identify the threat
- Go to the ID Ransomware website. Here is a direct link.
- Follow there in order to identify the specific virus you are dealing with.
IV – Decrypt your files
- Once you have identified the virus that has encrypted your files, you must acquire the respective tool to unlock your data.
- Open your browser and search for how to decrypt ransomware, look for the name of the one that has infected your system.
- With any luck, you’d be able to find a decryptor tool for your ransomware. If that doesn’t happen try Step V as a last ditch effort to save your files.
V – Use Recuva to restore files deleted by the virus
- Download the Recuva tool. This will help you restore your original files so that you won’t need to actually decrypt the locked ones.
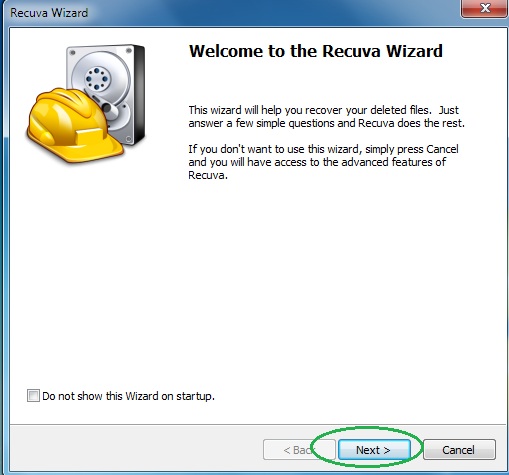
- Once you’ve downloaded the program, open it and select Next.
- Now choose the type of files you are seeking to restore and continue to the next page.
- When asked where your files were, before they got deleted, either use the option In a specific location and provide that location or choose the opt for the I am not sure alternative – this will make the program look everywhere on your PC.

- Click on Next and for best results, enable the Deep Scan option (note that this might take some time).
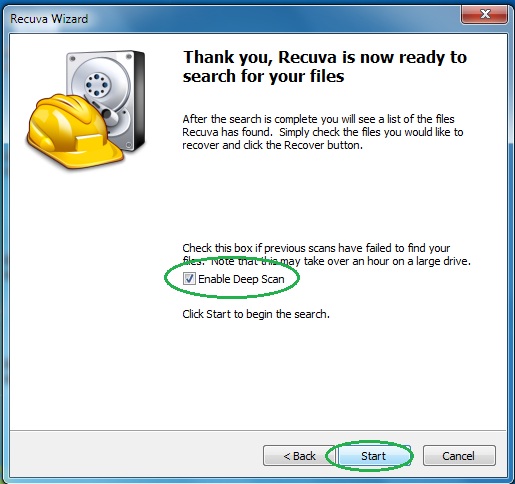
- Wait for the search to finish and then select which of the listed files you want to restore.






Leave a Reply