[bannerTop]
Welcome to our Ransomed@india Ransomware removal guide. The following instructions will aid you in removing the unwanted software from your PC for free.
Have you ever wondered what the most malicious computer infections are caused by? If yes, here’s your answer – the representatives of the Ransomware malicious family. These programs are very dangerous because of the way they operate and because they are capable of making your files or even your whole PC inaccessible.
Today’s article will be focused reviewing one particular virus from this category called Ransomed@india. You are going to read about all the characteristics of this virus throughout the paragraphs below. Beside that, there are some removal instructions added down below so that you can try to deal with this malware yourself. Good luck!
What characterizes Ransomware? What subcategories is it divided into?
Ransomware is the type of malware that seeks to lock something on the computer it infects. You should be aware of the fact that no matter what Ransomware tries to lock, it will afterwards ask for a ransom payment in exchange for restoring the access to the affected component of your device.
There are several types of Ransomware and we will explain to you what each of them is able to do below:
- There are Ransomware programs that could block your tablets’ and mobile devices’ screens. Here is what happens – a large ransom-demanding pop-up is displayed and it blocks your access to the affected screen. Because of the screen-wide pop-up, the user is made unable to do anything on their device as the whole interface of the device is covered by the pop-up. In this way the hackers want to force you to pay them the requested ransom so your screen becomes available again.
- Certain Ransomware versions are capable of affecting your PC and laptop desktops. The in which such Ransomware versions work is similar to the way mobile Ransomware viruses can lock the user’s display (as explained above) – by displaying a very big banner that makes you unable to interact with the computer. Once again, you are left powerless – rendered unable to access anything on your desktop and being expected to pay for reversing that.
The most common Ransomware category, which is the most horrifying one as well – the file-encrypting one:
Even with two other Ransomware subgroups, the data-encrypting viruses represent the most enormous and the most hazardous subcategory. Ransomed@india Ransomware, too falls under this malware category. Here’s what you can expect from such viruses:
- After their invasion in your system, such viruses may target particular file formats with their objective is the encryption of them all targeted files. The encryption process is completed in a few simple steps – first, the original file is copied and then deleted, leaving only the copy behind. The copies of the original files, however, are secured via an encryption code and you will need a specific key to access it which is exactly what you are later asked to pay for. The blackmailing is done via a large ransom notification which gives you all the details about the ransom payment methods, the amount that needs to be transferred and a possible deadline might be included as well.
- Such an extensive encryption process takes some time as well as a lot of system resources, which can sometimes make it easy to spot. In the case where something slows down your PC, check your Task Manager – a virus like Ransomed@india might have infected your machine.
What about Ransomed@india? Is there anything special about it?
In general, Ransomed@india is simply a standard form of data-encrypting Ransomware – it targets certain formats, encrypts the files that belong to those formats and then blackmails you into paying a ransom. This is all there is to this virus.
What you should know, though, is that Ransomed@india is extremely hard to handle. There are cases where even experts might find it totally futile to try to cope with such a malevolent program. Seen as it is hard to deal with, our team has attached a Removal Guide below. Perhaps that will do the job for you, even though we cannot give any promises.
What works against Ransomware is prevention and prevention only:
A 100% successful method against such a virus does actually exist – do NOT catch it at all. For that purpose, you need to know how it typically gets distribute. The most common Ransomware sources are the illegal movie-sharing web pages, all forms of spam (especially emails with attachments) as well as some malicious ads (Malvertising) and fake system requests which might all lead to the infection of your device.
If you want to keep your system in a good condition – stay away from these potential malware sources. Installing a good anti-malware/antivirus tool to help you prevent all kinds of contaminations is also a good recommendation. Moreover, in order to keep your OS healthy, be sure to always keep it updated to its latest version.
Ransomed@india Ransomware Removal
Here is what you need to do in order to remove a Ransomware virus from you computer.
I – Reveal Hidden files and folders and utilize the task manager
[bannerMiddle]
- Use the Folder Options in order to reveal the hidden files and folders on your PC. If you do not know how to do that, follow this link.
- Open the Start Menu and in the search field type Task Manager.
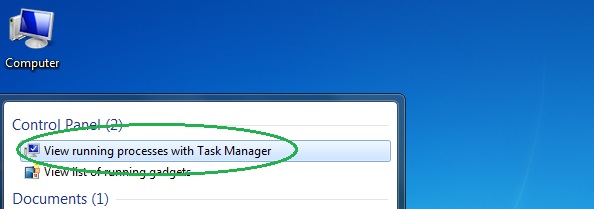
- Open the first result and in the Processes tab, carefully look through the list of Processes.
- If you notice with the virus name or any other suspicious-looking or that seems to consume large amounts of memory, right-click on it and open its file location. Delete everything in there.
[bannerMiddleSecond]

- Make sure that the hidden files and folders on your PC are visible, else you might not be able to see everything.
- Go back to the Task Manager and end the shady process.
II – Boot to Safe Mode
- Boot your PC into Safe Mode. If you do not know how to do it, use this guide/linked/.
III – Identify the threat
- Go to the ID Ransomware website. Here is a direct link.
- Follow there in order to identify the specific virus you are dealing with.
IV – Decrypt your files
- Once you have identified the virus that has encrypted your files, you must acquire the respective tool to unlock your data.
- Open your browser and search for how to decrypt ransomware, look for the name of the one that has infected your system.
- With any luck, you’d be able to find a decryptor tool for your ransomware. If that doesn’t happen try Step V as a last ditch effort to save your files.
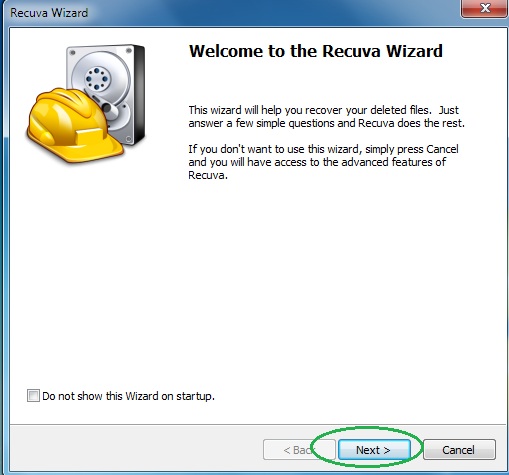
V – Use Recuva to restore files deleted by the virus
- Download the Recuva tool. This will help you restore your original files so that you won’t need to actually decrypt the locked ones.
- Once you’ve downloaded the program, open it and select Next.
- Now choose the type of files you are seeking to restore and continue to the next page.
- When asked where your files were, before they got deleted, either use the option In a specific location and provide that location or choose the opt for the I am not sure alternative – this will make the program look everywhere on your PC.

- Click on Next and for best results, enable the Deep Scan option (note that this might take some time).
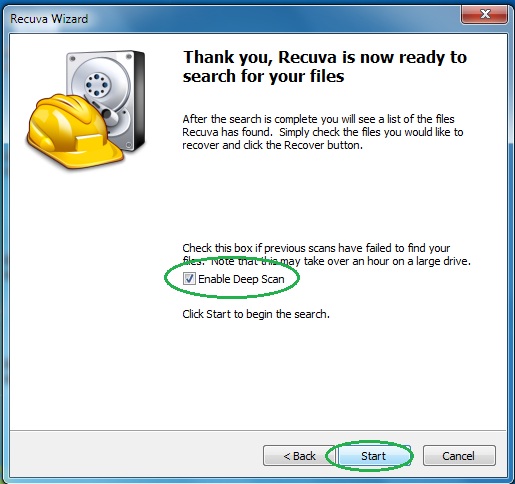
- Wait for the search to finish and then select which of the listed files you want to restore.






Leave a Reply