[bannerTop]
The following guide was created to help Ransomware victims recover .Osiris encrypted files and help them remove the .Osiris File Virus itself (it remains in their system).
Welcome to our article about one of the most recent entries to the Ransomware virus family. The name of the new virus is .Osiris File Virus and in this article we will provide you with some very important information regarding this type of malicious programs and what you need to do in order to prevent Ransomware from getting inside your PC and encrypting your files. We also have a removal guide that you can refer to if the noxious .Osiris File Virus has already gotten inside your machine and locked your data. However, our advice for you, regardless of whether you have been attacked by the Ransomware or you are simply looking for more information, is to read all paragraphs. The tips and guidelines that we have provided can be the difference between having a safe and well-secured PC or one that has been infected by some nasty malware such as the one we are going to be talking about today.
.Osiris File Virus and encryption
Ransomware viruses are infamous for their abuse of the encryption technique that they use to render people’s files inaccessible. The method itself is not malicious and is widely used by many other legal programs as a way of protecting their files. The majority of security programs are unable to distinguish encryption coming from legit software and one that is executed by Ransomware. This makes it incredibly difficult to detect this particular type of viruses. Thus, they are able to remain hidden and unnoticed throughout the duration of the process. Once it’s over, the only way to access your files is to provide your PC with the decryption key. At this point, the Ransomware itself will display a notification on your screen, informing you that ransom must be paid if you want to obtain the key for your files. Instructions on how to carry out the transfer are provided within the Ransomware note.
Why it’s important to be vigilant
Most viruses rely on the lack of the user’s attention to detail, both when they infect the computer and during the time they are following their agenda. The same can be said with regards to Ransomware. The Ransomware might not get detected by your security tool, but it’s technically possible that you spot the infection yourself. The process of encryption takes time and free disk space and also requires considerable amounts of RAM and CPU. This is because your files do not get encrypted straight away. They first get copied by the virus. Those copies are the actual ones that are locked by the virus’ code. Though they are intact and absolutely the same as your initial files, you cannot access them without the key. After this first stage has been finished, your original documents are deleted. Obviously, this usually does not happen instantly, especially if you have a lot of personal data on your hard-drive. This gives you a window of opportunity to spot the virus. You just need to be vigilant and take notice of your PC’s behavior and the system resources that are being used. If a lot of RAM and CPU is being consumed, but you cannot see a visible cause for that or if they are being used by some suspicious process in your Task Manager, then it’s best if you immediately shut down your PC and have it examined by an IT specialist. Also, if you suspect a Ransomware infection, avoid connecting any external devices such as smartphones, flash memory sticks or external HDD’s since the files stored on them might too get encrypted by .Osiris File Virus.
Why paying the money is a bad idea?
If the ransom demand is not overly high, you might think to yourself that this might not be such a bad idea after all. However, know that there is absolutely no way of knowing if you are actually going to get the decryption key after you’ve transferred the money. On top of that, if you obey to the hacker’s demands, you will effectively encourage them to keep on attacking more and more computers with the virus, since it earns them money. We always advise our readers to look for another way. This is also why we have developed our removal guide. We cannot guarantee that it would help in every instance of a Ransomware infection, but it is surely worth the shot, so go ahead and give it a try.
PC security tips
The next list of tips and guidelines will help you provide your PC with enhanced protection against any potential Ransomware attacks, so make sure you remember and use the advice we are about to give you.
- Do not visit websites that have a bad reputation and/or are illegal. Being cautious and responsible while surfing the internet is crucial when it comes to protecting your system from malware attacks.
- Create a backup copy of all data files that you consider important, so that even if the original ones get attacked by .Osiris File Virus, you’d still have their accessible copies in a safe place.
- Do not underestimate the importance of good anti-virus software. Some of them already have anti-ransomware features and they can help you fend off backdoor viruses that are often used to provide the Ransomware direct access to your PC.
- Delete any suspicious e-mails without even opening them, since they might be carriers of .Osiris File Virus.
SUMMARY:
| Name | .Osiris File Virus |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Heavy CPU, RAM and free HDD space usage during the encryption period, often causing your PC to experience slow-downs. |
| Distribution Method | Malicious messages/e-mails, illegal sites with sketchy/harmful contents, backdoor viruses. |
.Osiris File Virus Removal
Here is what you need to do in order to remove a Ransomware virus from you computer.
[bannerMiddle]
I – Reveal Hidden files and folders and utilize the task manager
- Use the Folder Options in order to reveal the hidden files and folders on your PC. If you do not know how to do that, follow this link.
- Open the Start Menu and in the search field type Task Manager.
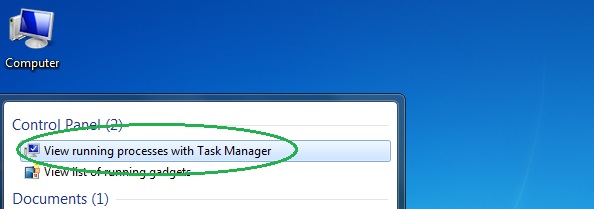
- Open the first result and in the Processes tab, carefully look through the list of Processes.
- If you notice with the virus name or any other suspicious-looking or that seems to consume large amounts of memory, right-click on it and open its file location. Delete everything in there.

- Make sure that the hidden files and folders on your PC are visible, else you might not be able to see everything.
- Go back to the Task Manager and end the shady process.
II – Boot to Safe Mode
- Boot your PC into Safe Mode. If you do not know how to do it, use this guide/linked/.
III – Identify the threat
- Go to the ID Ransomware website. Here is a direct link.
- Follow there in order to identify the specific virus you are dealing with.
IV – Decrypt your files
- Once you have identified the virus that has encrypted your files, you must acquire the respective tool to unlock your data.
- Open your browser and search for how to decrypt ransomware, look for the name of the one that has infected your system.
- With any luck, you’d be able to find a decryptor tool for your ransomware. If that doesn’t happen try Step V as a last ditch effort to save your files.
V – Use Recuva to restore files deleted by the virus
[bannerMiddleSecond]
- Download the Recuva tool. This will help you restore your original files so that you won’t need to actually decrypt the locked ones.
- Once you’ve downloaded the program, open it and select Next.
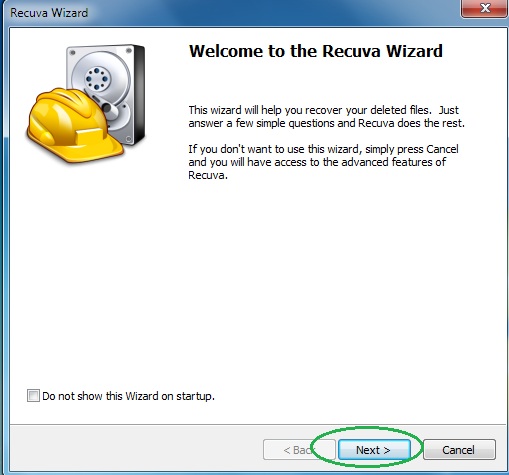
- Now choose the type of files you are seeking to restore and continue to the next page.
- When asked where your files were, before they got deleted, either use the option In a specific location and provide that location or choose the opt for the I am not sure alternative – this will make the program look everywhere on your PC.

- Click on Next and for best results, enable the Deep Scan option (note that this might take some time).
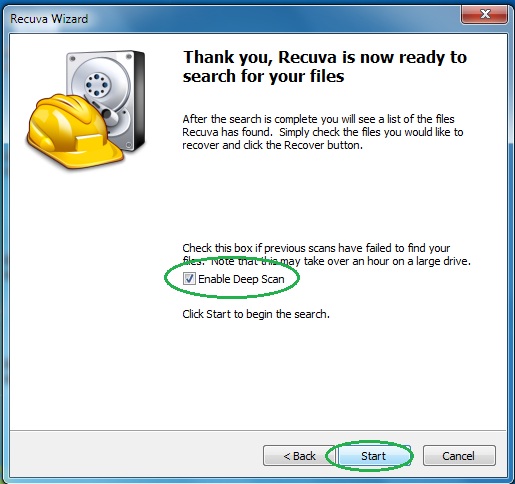
- Wait for the search to finish and then select which of the listed files you want to restore.






Leave a Reply