[bannerTop]
Welcome to our File Spider Virus Ransomware removal guide. The following instructions will aid you in removing the unwanted software from your PC for free.
When we discuss malware infections, the largest number of them is reportedly caused by versions of Trojan horse viruses. Despite that, the most dangerous and hard-to-remove infections ever recorded should be blamed on another virus category – Ransomware. This is the basic reason why the article below exists – to help you learn more about the features and effects of one exact Ransomware member: Spider. We will advise you on how to handle this incredibly malicious infection in the most sensible way. Speaking in general, Spider is representative of the so-called file-encrypting Ransomware subcategory, which sneaks into your PC without asking for your permission; and after that makes you unable to access the files this virus blocks. In the following stages of the infection, this malicious piece of software gives you a message letting you know that the scammers behind this program expect you to pay a ransom for the safe and total decryption of the affected files.

What you should expect from a threat like File Spider:
This particular malware program usually conducts an extensive data-encoding process just as any typical file-encrypting Ransomware does. Typically, the encryption process occurs after the malware has already determined which data exactly you seem to value most. Actually, not only does Spider define the files that are to be encoded, but it also gathers the names and locations of that data in order to encrypt it one by one after that. The last stage of the infection is to receive the frightening alert message, stating that you owe some hackers a ransom and you are obliged to pay it before an exact deadline. Quite unfortunately, to our disappointment nearly nothing can be done after the encryption process has been fully completed. The file-encoding viruses are awfully difficult and nerve/ time-consuming to deal with. In fact, even if you go and ask somebody with experience to help you with that virus, the expert may find it too risky or complex to really handle this kind of an infection.
Fully recovering from this kind of infection, though, is not always impossible. Sometimes some tips and knowledge really help. You simply have to seek different options before you make a decision of whether to pay the demanded money to the blackmailers. Such an alternative may be purchasing some specialized software to cure and remove the contamination. However, be cautious as there aren’t that many of these programs out there and you might come across a fake one, which is itself malicious. What’s more, you might want to see our special Removal Guide. Maybe the steps there will be what it takes to safely and successfully deal with the virus. Still, we cannot promise the total and successful decryption of the affected data.
Ransomware sources:
Hackers might spread all such horrifying viruses via many kinds of distribution methods:
- Emails/ their attachments: The ones from unfamiliar or shady addresses should be especially avoided as possible Ransomware sources. Moreover, the attachments of such letters could be contaminated. What we can suggest is that you should stay away from all the emails from unfamiliar sources, and their attachments in general.
- Fake update requests: Another very likely source of Ransomware are the fake update requests you could receive on a daily basis. They are not really produced by your OS, but behave in the same way as any other system request. The difference is that they are just the projections of a virus and you had better never click on any of them.
- Malvertising (contaminated online ads): Malvertising is another very common Ransomware source. Actually, your personal computer might automatically get infected by a malicious program in case you click on a contagious ad, no matter whether you do it intentionally or unintentionally.
Some extra tips:
- Don’t be hasty and don’t hurry to pay the demanded ransom immediately after you get the ransom notification. Seek for other possible solutions. Your files are already danger; why risk your money as well?
- Attempt to simply avoid all possible sources of this awful software. Always try to stay away from them all and finally, you will get used to that process.
- Make sure to do a little research and search for the most effective program – we promise that this is essential for the development of some really good prevention habits.
File Spider Virus Ransomware Removal
Here is what you need to do in order to remove a Ransomware virus from you computer.
I – Reveal Hidden files and folders and utilize the task manager
[bannerMiddle]
- Use the Folder Options in order to reveal the hidden files and folders on your PC. If you do not know how to do that, follow this link.
- Open the Start Menu and in the search field type Task Manager.
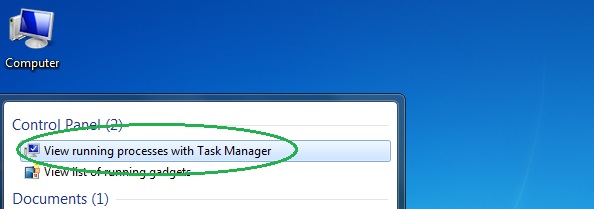
- Open the first result and in the Processes tab, carefully look through the list of Processes.
- If you notice with the virus name or any other suspicious-looking or that seems to consume large amounts of memory, right-click on it and open its file location. Delete everything in there.
[bannerMiddleSecond]

- Make sure that the hidden files and folders on your PC are visible, else you might not be able to see everything.
- Go back to the Task Manager and end the shady process.
II – Boot to Safe Mode
- Boot your PC into Safe Mode. If you do not know how to do it, use this guide/linked/.
III – Identify the threat
- Go to the ID Ransomware website. Here is a direct link.
- Follow there in order to identify the specific virus you are dealing with.
IV – Decrypt your files
- Once you have identified the virus that has encrypted your files, you must acquire the respective tool to unlock your data.
- Open your browser and search for how to decrypt ransomware, look for the name of the one that has infected your system.
- With any luck, you’d be able to find a decryptor tool for your ransomware. If that doesn’t happen try Step V as a last ditch effort to save your files.
V – Use Recuva to restore files deleted by the virus
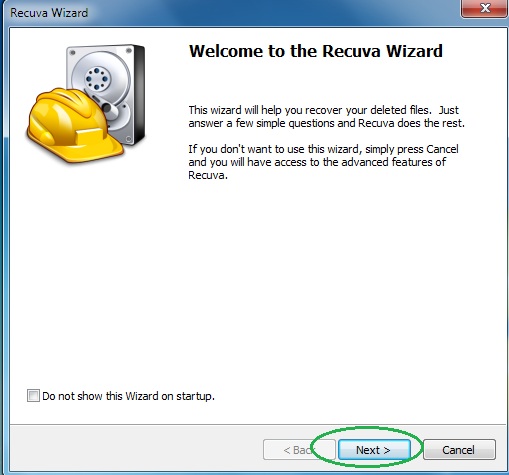
- Download the Recuva tool. This will help you restore your original files so that you won’t need to actually decrypt the locked ones.
- Once you’ve downloaded the program, open it and select Next.
- Now choose the type of files you are seeking to restore and continue to the next page.
- When asked where your files were, before they got deleted, either use the option In a specific location and provide that location or choose the opt for the I am not sure alternative – this will make the program look everywhere on your PC.

- Click on Next and for best results, enable the Deep Scan option (note that this might take some time).
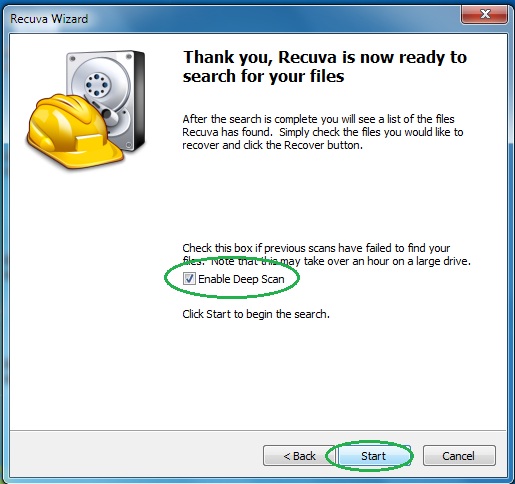
- Wait for the search to finish and then select which of the listed files you want to restore.






Leave a Reply