[bannerTop]
Welcome to our Cry9 Ransomware removal guide. The following instructions will aid you in removing the unwanted software from your PC for free.
Ransomware infections are really harmful and very difficult to deal with, that’s why they require a good understanding and an alternative approach. On this page, we are going to speak about the specifics, the infection methods and the harmful effects of one of the advanced versions of Ransomware called Cry9 Ransomware, which is specialized in secretly encrypting your files and then blackmailing you to pay ransom to decrypt them. The result of such a harmful infection could be the denied access to your valuable data and the loss of your money, in case that you risk and decide to pay the required ransom to the criminals, who stand behind the threat. If you have been infected, and you are looking for some alternative ways to counteract the effects of Cry9 Ransomware and its malicious encryption, then, you have come to the right place. There are a few options that can eventually help you deal with the Ransomware and in the lines below, we are going to tell you all of them. We cannot tell you how effective they will be in your case, but it is worth trying everything possible to recover from the infection without paying any ransom right? So, in this regard, in the next lines, we are going to give you some free instructions, neatly organized in a removal guide, which may help you remove Cry9 Ransomware from your system and do something about the encrypted files by trying to regain the access to some of them.
Cry9 Ransomware sneaks in undetected and uses encryption to lock your data!
Cry9 Ransomware is a Ransomware cryptovirus, which is used in a malicious file-encrypting blackmail scheme, which is very popular in criminal circles nowadays. By applying a secret encryption algorithm to all the files, found on the infected machine, this threat basically locks them out and doesn’t let the user access them unless he pays a certain amount of money in ransom. The hackers, who stand behind Cry9 Ransomware, usually have a special decryption key, which is the only thing capable of reversing the encryption caused by the Ransomware and bring the affected files back to normal. But, as you may guess, they would not give it to you unless you strictly fulfill their ransom demands, which you can find in a disturbing ransom note right after the malicious encryption has taken place.
Most security software fails to detect the encryption as malicious!
Unfortunately, almost in all cases, Ransomwareinfections tend to come like a bolt from the blue. Users are hardly ever capable of noticing any symptoms or specific signs that can identify that they have been infected with Cry9 Ransomware and all of their files are getting silently encrypted. The main reason for the stealthy way that this threat can attack you is the fact that its encryption is usually not recognized as malicious by most antivirus or security software. Therefore, it manages to lock the users’ files without being disturbed and the victims come to know about it only when the ransom note appears on their screen.
I don’t want to pay the ransom, what should I do?
Your files have been locked, but you are currently trying to work around the Ransomware without paying the ransom? Good! This is a firm step against this nasty blackmail scheme and a far better decision than giving money to some unscrupulous hackers in the hopes of getting some mysterious decryption key. What we can suggest as an alternative is to remove Cry9 Ransomware from your system and try some of the other possible options that may eventually help you restore some of your encrypted files. To start with, you can scroll down and follow the steps in the removal guide below, which can help you locate and safely remove the Ransomware. Make use also of the file restoration tips included there, because they may potentially work out in your case, if not in all of them. Another safe option is to search for some specialized decryption tool or ask a professional to help you handle the infection. Keep in mind, though, that regardless of the professionalism, the tools, and the removal guides, there is no universal solution that can promise you a full recovery from such an attack, so trying every possible alternative to paying the criminals is the best you can do.
How to reduce the chances of getting infected?
The chances of catching Ransomware like Cry9 Ransomware are very high if you frequently interact with sketchy web content, shady sites, pirated materials, intrusive ads, banners, and pop-ups or some insecure web locations. Your email inbox may also contain transmitters of this infection, which usually come in the form of a well camouflaged Trojan horse viruses. That’s why it is best if you stay away from spam and don’t get tempted to click and open every link or attachment that appears on your screen or comes your way. To boost the safety level of your system, make sure you update it to the latest version and security patches. This will ensure that there are no vulnerabilities, which threats like Cry9 Ransomware or other nasty viruses can exploit. Another important thing is to have reliable antivirus software and run regular scans with it to prevent tricky malware, especially Trojans, from sneaking inside undetected and delivering Ransomware to your machine. Also, just for extra safety, always back up all the valuable data that you keep on your PC, because this is one sure way to keep it safe in case of a Ransomware attack.
SUMMARY:
| Name | Cry9 Ransomware |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
Cry9 Ransomware Removal
Here is what you need to do in order to remove a Ransomware virus from you computer.
I – Reveal Hidden files and folders and utilize the task manager
[bannerMiddle]
- Use the Folder Options in order to reveal the hidden files and folders on your PC. If you do not know how to do that, follow this link.
- Open the Start Menu and in the search field type Task Manager.
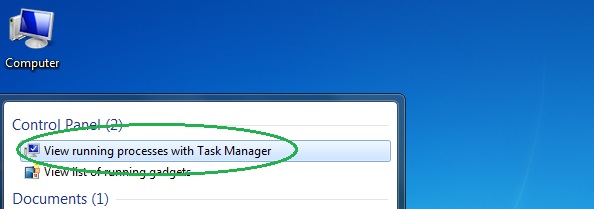
- Open the first result and in the Processes tab, carefully look through the list of Processes.
- If you notice with the virus name or any other suspicious-looking or that seems to consume large amounts of memory, right-click on it and open its file location. Delete everything in there.
[bannerMiddleSecond]

- Make sure that the hidden files and folders on your PC are visible, else you might not be able to see everything.
- Go back to the Task Manager and end the shady process.
II – Boot to Safe Mode
- Boot your PC into Safe Mode. If you do not know how to do it, use this guide/linked/.
III – Identify the threat
- Go to the ID Ransomware website. Here is a direct link.
- Follow there in order to identify the specific virus you are dealing with.
IV – Decrypt your files
- Once you have identified the virus that has encrypted your files, you must acquire the respective tool to unlock your data.
- Open your browser and search for how to decrypt ransomware, look for the name of the one that has infected your system.
- With any luck, you’d be able to find a decryptor tool for your ransomware. If that doesn’t happen try Step V as a last ditch effort to save your files.
V – Use Recuva to restore files deleted by the virus
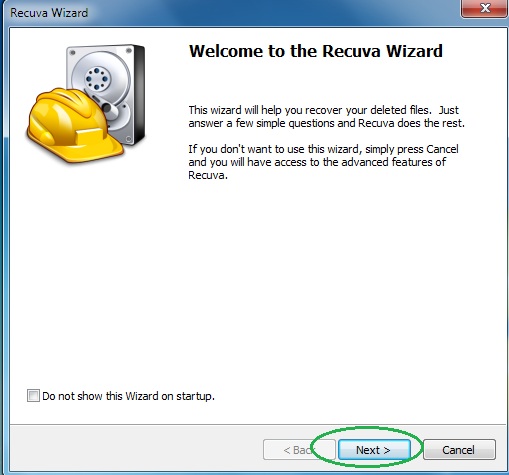
- Download the Recuva tool. This will help you restore your original files so that you won’t need to actually decrypt the locked ones.
- Once you’ve downloaded the program, open it and select Next.
- Now choose the type of files you are seeking to restore and continue to the next page.
- When asked where your files were, before they got deleted, either use the option In a specific location and provide that location or choose the opt for the I am not sure alternative – this will make the program look everywhere on your PC.

- Click on Next and for best results, enable the Deep Scan option (note that this might take some time).
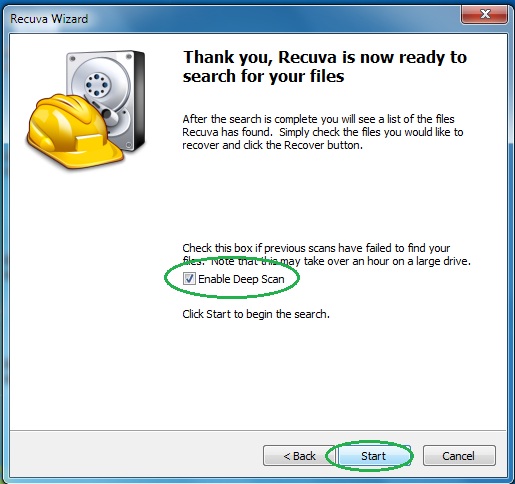
- Wait for the search to finish and then select which of the listed files you want to restore.






Leave a Reply