[bannerTop]
Welcome to our .arrow Ransomware removal guide. The following instructions will aid you in removing the unwanted software from your PC for free.
Though there are many different malware categories out there, few of them can be as devastating and as problematic as the type of PC viruses collectively known as Ransomware. Those truly are some of the nastiest and most unpleasant software virus forms and you need to be well acquainted with their capabilities.
Basically, that’s the reason why this article has been published. Really, we strive to assist you in finding out more about the consequences coming from one particular Ransomware version – .arrow.

.arrow is a representative of the awful file-encrypting Ransomware subcategory, which is capable of sneaking into your device and after that – rendering you unable to access your personal data files by using an encryption code to lock them. Following that, this malicious software normally sends a message to you to inform you about what the hackers behind this program want you to do. Usually they are after a ransom that you are blackmailed into paying – if the money gets paid, you’d supposedly receive the key that will allow you to bypass the encryption.
What should be expected from a virus like .arrow Ransomware:
Just as any other file-encrypting Ransomware virus may do, this exact virus could perform a file-locking process. Typically, the encryption takes place right after this malicious program has already determined which data files it is going to lock-up. Really, not only can the virus define the data to-be-encrypted, but it may also create a list containing all of the details about the selected files. During the following stage of the infection you get the scary alert message, which states that you “owe” some cyber-criminals a ransom and you have to pay it before an exact deadline comes.
Actually, it is technically possible to notice the encryption process while it is still ongoing. Nonetheless, it is far more likely that the data encryption happens without you noticing anything.
In spite of that, you could be among the lucky ones, and if you happen to notice a unfamiliar, shady-looking process taking place in your Task Manager, please turn off your device, and contact an expert for assistance. Such an unknown process might be a Ransomware virus encoding some essential data.
Pretty much nothing could be done in case the encryption process has ended. The file-encrypting viruses are very hard to deal with. Indeed – even the professionals in that field may find it very complicated to cope with such viruses without paying the demanded ransom, and recover the hijacked files in the end. Moreover, we should be realistic here – there really are rather slim chances of success in certain cases. That said, you shouldn’t lose hope – there are various potential solutions and we are about to present you with some of them.
Normally, it is a wise idea to try to remove the infection yourself. Search for other possibilities before you decide to pay the money the hackers want from you. For instance, you can try asking a specialist for advice and some special kind of know-how. And you could as well try some special software for the purpose of removing the contamination. Also, you could always try our Removal Guide. Maybe it will be what you need to set your files free and deal with the virus. However, we cannot really promise you such a happy turn of the events – nothing is guaranteed when it comes to Ransomware.
The places where Ransomware could be found:
Online scammers might spread such horrifying viruses in many different ways:
- Inside emails (their attachments also): Many of the e-letters, especially the ones from unfamiliar senders, may be used for transporting Ransomware. Moreover, the attachments of such emails could as well be contagious. Our basic tip for you is to avoid all the letters from sources you do not recognize, and stay away from their attachments as well.;
- With the help of malicious pop-ups and other ads: Malvertising is one more common source of Ransomware. Your PC might automatically catch some malware, as soon as you click on a contagious ad, no matter how that happens – intentionally or unintentionally. ;
- The fake system requests might be a source: Another likely source of Ransomware might be the fake system requests – the ones that are not generated by your OS, however, which serve the same aim as the aforementioned malicious ads. Still, such requests may indeed resemble the original ones. In order to avoid such threats as .arrow, ensure that you update your system manually and search for updates yourself whenever you have the chance to do so.
Some basic advice in general:
- Ensure that you do NOT pay the required ransom immediately after you see the notification. Seek another possible solution instead. Your data is already in danger; remain wise and do not risk your money without having tried anything else.
- Make sure that you always avoid all possible sources of this terrible malware.
- Pay for the license of the most efficient program against malware you can find. It might require some research but trying to find the most efficient software is something we promise you will never ever regret.
.arrow Ransomware Removal
Here is what you need to do in order to remove a Ransomware virus from you computer.
I – Reveal Hidden files and folders and utilize the task manager
[bannerMiddle]
- Use the Folder Options in order to reveal the hidden files and folders on your PC. If you do not know how to do that, follow this link.
- Open the Start Menu and in the search field type Task Manager.
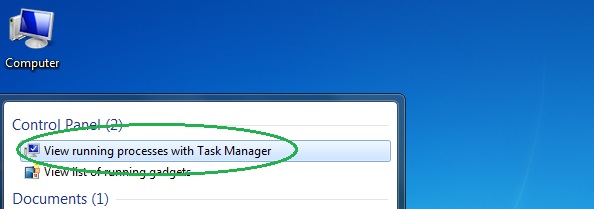
- Open the first result and in the Processes tab, carefully look through the list of Processes.
- If you notice with the virus name or any other suspicious-looking or that seems to consume large amounts of memory, right-click on it and open its file location. Delete everything in there.
[bannerMiddleSecond]

- Make sure that the hidden files and folders on your PC are visible, else you might not be able to see everything.
- Go back to the Task Manager and end the shady process.
II – Boot to Safe Mode
- Boot your PC into Safe Mode. If you do not know how to do it, use this guide/linked/.
III – Identify the threat
- Go to the ID Ransomware website. Here is a direct link.
- Follow there in order to identify the specific virus you are dealing with.
IV – Decrypt your files
- Once you have identified the virus that has encrypted your files, you must acquire the respective tool to unlock your data.
- Open your browser and search for how to decrypt ransomware, look for the name of the one that has infected your system.
- With any luck, you’d be able to find a decryptor tool for your ransomware. If that doesn’t happen try Step V as a last ditch effort to save your files.
V – Use Recuva to restore files deleted by the virus
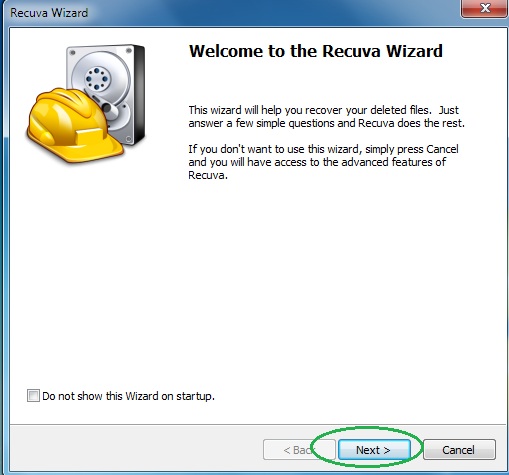
- Download the Recuva tool. This will help you restore your original files so that you won’t need to actually decrypt the locked ones.
- Once you’ve downloaded the program, open it and select Next.
- Now choose the type of files you are seeking to restore and continue to the next page.
- When asked where your files were, before they got deleted, either use the option In a specific location and provide that location or choose the opt for the I am not sure alternative – this will make the program look everywhere on your PC.

- Click on Next and for best results, enable the Deep Scan option (note that this might take some time).
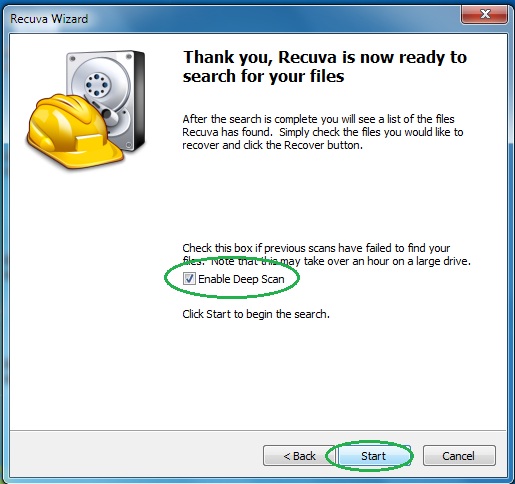
- Wait for the search to finish and then select which of the listed files you want to restore.






Leave a Reply